Monday 19 December, 2016, 13:59 - Amateur Radio, Broadcasting, Spectrum Management
Posted by Administrator
Posted by Administrator
 Wireless Waffle last discussed the issue of interference to and from wireless car keys and other similar devices back in 2013, but the topic has cropped up here almost since time immemorial. The original articles discussed the fact that the frequency band used for these devices (around 433.925 MHz) was shared with radio amateurs and that not only were the radio amateurs suffering from interference but that there were cases of car users getting stuck either unable to lock or unlock their cars due to nearby amateur radio transmissions.
Wireless Waffle last discussed the issue of interference to and from wireless car keys and other similar devices back in 2013, but the topic has cropped up here almost since time immemorial. The original articles discussed the fact that the frequency band used for these devices (around 433.925 MHz) was shared with radio amateurs and that not only were the radio amateurs suffering from interference but that there were cases of car users getting stuck either unable to lock or unlock their cars due to nearby amateur radio transmissions.But it seems that the situation has changed and that criminals have cottoned on to the fact that it's possible to jam the transmissions between cars and their keys to their benefit. The BBC reports that thieves in a car park in Berkshire had been 'using car key jammers' and also provides useful advice on the impact and implications of car key jammers.
Now far be it for Wireless Waffle to condone such activities, but it is so brain-achingly simple, and mind-bogglingly cheap, to jam these signals, that it's a surprise that it has taken criminals so long to figure out how to do it.
 Transmissions from car key fobs normally use either amplitude modulation or fairly crude frequency modulation and the transmitters have a power level of no more than 10 milliWatts. The receivers in the vehicles are manufactured to a price point of around 50 pence and are woefully inadequate at protecting against interference. Thus, a strong enough signal on the same frequency as the car key transmitter (or indeed on a neighbouring one) will overwhealm the low power transmission from the keys. A 40 Watt transmitter (4000 times stronger than the signal from the keys) operating in the same band can be purchased on-line for little more than GBP100.
Transmissions from car key fobs normally use either amplitude modulation or fairly crude frequency modulation and the transmitters have a power level of no more than 10 milliWatts. The receivers in the vehicles are manufactured to a price point of around 50 pence and are woefully inadequate at protecting against interference. Thus, a strong enough signal on the same frequency as the car key transmitter (or indeed on a neighbouring one) will overwhealm the low power transmission from the keys. A 40 Watt transmitter (4000 times stronger than the signal from the keys) operating in the same band can be purchased on-line for little more than GBP100. Such a transmitter would be a brute force way to stop the receiver in the car from being able to hear the signal from the key. This would stop the key from being able to lock the car, meaning that an unsuspecting driver could get out of the car and casually press the button on their key and walk away without listening for the corresponding 'clunk' of the car locking, not realising that the car has not locked. This would clearly leave the car unlocked and easy pickings for a thief.
In principal it would be easy to go one stage further. With a simple receiver it would be possible to record the transmission from the key, and using a low power transmitter, it would be feasible to re-create the signal. In this case, it would be possible for a criminal to unlock a car after it had been safely locked by the driver. Don't say we didn't warn you.
 This is not just possible for car keys, but for any devices which operate in a similar manner. The 433 MHz band used for these devices is replete with a variety of signals from wireless devices such as garage doors, parking barriers and devices for which an attack would be less significant such as weather stations and doorbells. The chart below (known as a waterfall chart) shows, from top to bottom, around 2 minutes of time, and from left to right, the middle portion of the 433 MHz band. A wide range of different transmissions are shown as bars or dots and it is clear there's plenty afoot here despite the transmission area of the devices being very small and thus the limited number of devices in range of the receiver used to perform this scan.
This is not just possible for car keys, but for any devices which operate in a similar manner. The 433 MHz band used for these devices is replete with a variety of signals from wireless devices such as garage doors, parking barriers and devices for which an attack would be less significant such as weather stations and doorbells. The chart below (known as a waterfall chart) shows, from top to bottom, around 2 minutes of time, and from left to right, the middle portion of the 433 MHz band. A wide range of different transmissions are shown as bars or dots and it is clear there's plenty afoot here despite the transmission area of the devices being very small and thus the limited number of devices in range of the receiver used to perform this scan. 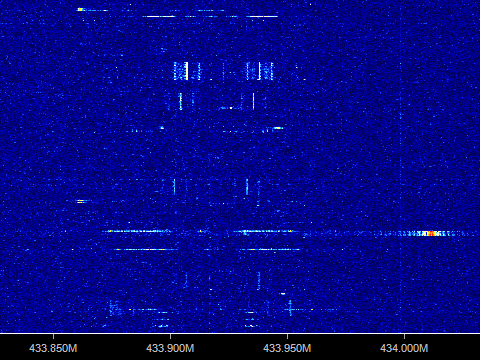
As the number and variety of wireless devices increases, in particular as we progress to the world of the 'Internet of Things' in which there will be sensors and actuators everywhere, it is clear that the security of wireless connections needs beefing up. If you are concerned about your car being 'hacked' by criminals, the best way is to disable the convenience of the wireless key locks and return to the old-fashioned technique of putting the key for your car into the door. Sadly, some modern cars don't actually have this feature any more!
3 comments
( 1133 views )
| permalink
| 



 ( 2.9 / 9631 )
( 2.9 / 9631 )




 ( 2.9 / 9631 )
( 2.9 / 9631 )

